Professional services based on outstanding security engineering.
SECURITY
ENABLEMENT
Secure the device life cycle. TrustiPhi takes clients like Micron through architecture, design, and deployment to build hardware-level security into products.
If you need a detailed roadmap to multi-layer security for fleets of IoT devices, you have come to the right place.
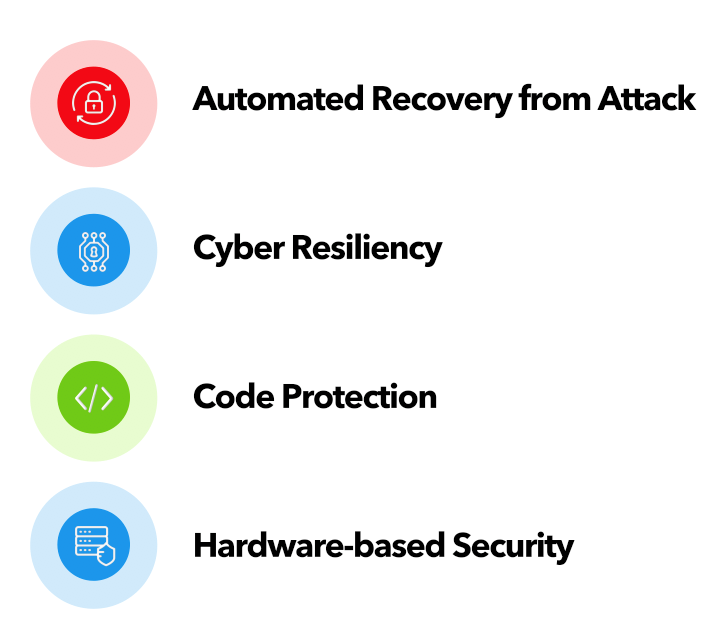
ADVANCED SECURITY
ARCHITECTURE & DESIGN
- Chip-level, system-level and platform-level security architecture and design
- Security design review and threat analysis
- Platform security subsystem design, testing and validation
- Cross-platform architecture and design
SOFTWARE & FIRMWARE DEVELOPMENT
We have led the development efforts for security software and firmware that have shipped on hundreds of millions of systems. We can ensure that your solutions are built securely, on time and under budget.
AUTHENTA RELATED
SERVICES
TrustiPhi has the skills and Authenta expertise to help your Product Development and Engineering teams build and execute a complete strategy to maximize the business and security value of embedding Micron Authenta in your products.
Technology leaders and product development groups engage TrustiPhi to add the latest, strongest security and get to market faster with less cost and risk.

Advanced Security Architecture & Design
We help our clients build their security foundation for:
- Mobile, embedded, control, appliance, gateway, PC, server and connected devices
- Secure protection mechanisms and cryptographic solutions
- Provisioning solutions for secure supply chain management
Security Assessment and Review
Take stock, match up to compliance and market requirements, and find the path to security enablement of your products that will meet your business goals and timetable. Avoid locking into the wrong technology choice and reduce risks.
Some of the most highly respected technology providers and users in critical infrastructure engage TrustiPhi for a short-term, structured process of assessing security gaps and opportunities in their products and systems. Learn more…

Authenta Related Services
If you seek a major product differentiation and advantage that would build upon Micron Authenta capabilities, TrustiPhi can strategize, evaluate, and execute the development to completion and QA, leveraging our unmatched expertise (outside of Micron) in Authenta. Learn more…
Technology Integration
Multi-layer defense is often most effective when attackers must guess which combination of defensive strategies and components they are up against. This integration is not easy – super strong defense never is – and we offer specialized experienced and tools we have developed to structure and speed up results.

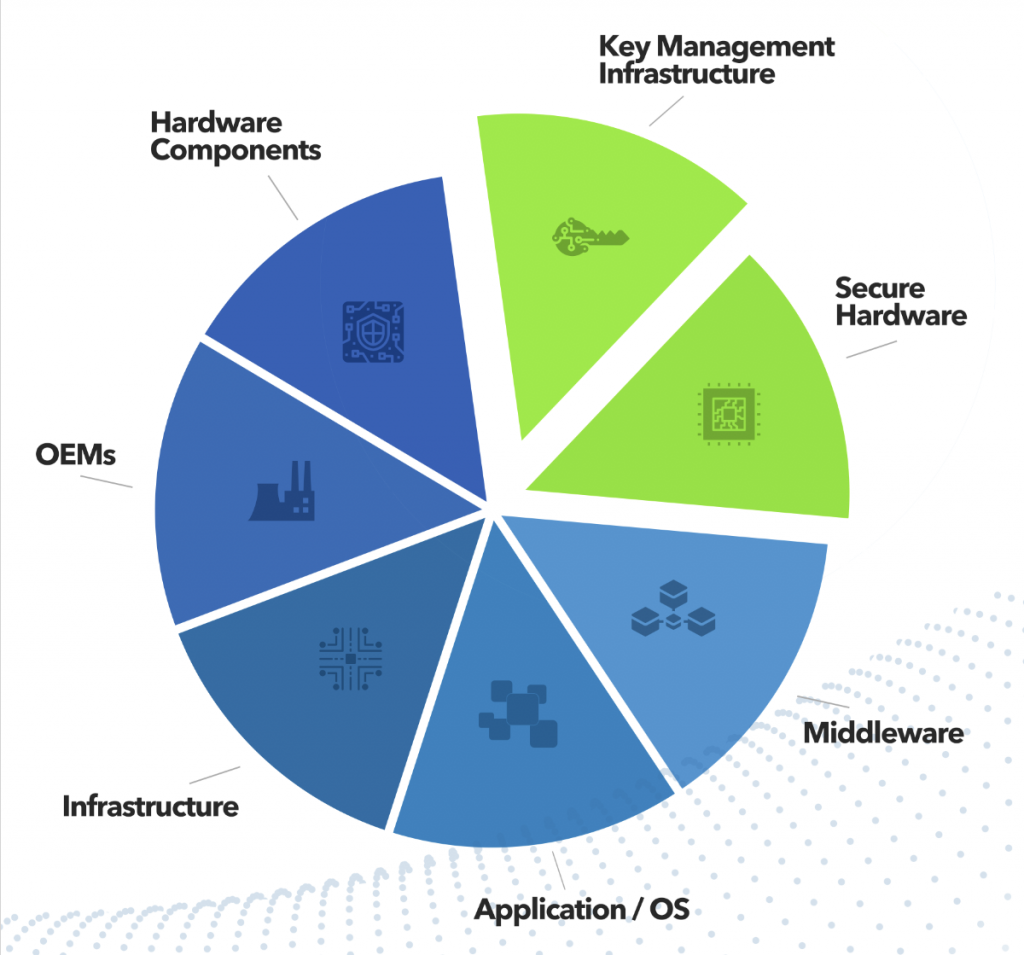
TrustiPhi is among the most capable resources worldwide in the specialized areas where we assist engineering clients. We also work with carefully selected technology partners.
Our customers trust us to recommend and implement the right combination of technologies to meet their business goals, technical needs, and compliance mandates, based on our experience with the security ecosystem:
- Hardware components and security modules (TPM, SOC)
- Key management infrastructure
- Middleware
- Applications and operating systems
- Architecture and infrastructure